This story appeared in the November 2020 issue as "Cracking the 414s." Subscribe to Discover magazine for more stories like this.
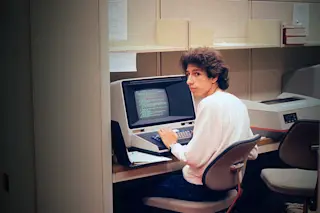
In the 1983 techno-thriller WarGames, David Lightman, played by a fresh-faced Matthew Broderick, sits in his bedroom, plunking away on a boxy computer using an 8-bit Intel processor. As text flashes across the screen, David’s face lights up; he believes he’s hacking into a video game company, but the unwitting teenager is actually facing off against a military supercomputer. “Shall we play a game?” the computer asks ominously. In the film, the subsequent showdown triggers a countdown to World War III.
The same year the film was released, a group of teenagers and young adults from Milwaukee were playing a game of their own. Much like Broderick’s character, these suburban tech savants — who dubbed themselves the 414s — hacked into large, networked computer systems used by high-profile organizations, looking for new games to play. And similarly, what started out as innocuous fun had some very real consequences. The group eventually was caught by the FBI for raiding around a dozen government and industry systems. Among these were Memorial Sloan Kettering Cancer Center and the Los Alamos National Laboratory, a nuclear weapons research site that produced atomic bombs used during World War II.

For much of the American public, the 1983 Matthew Broderick/Ally Sheedy film WarGames and the 414s’ antics were their first introductions to the idea of “hackers.” (Credit: AA Film Archive/Alamy)
AA Film Archive/Alamy
While the 414s’ antics didn’t spark a nuclear conflict, they did ignite a national conversation on computer security — long before cyberwarfare made headlines and modern-day hackers like Julian Assange became household names. Plus, the media frenzy fueled by the group alerted U.S. legislators that new laws were needed to combat computer crime.
Ultimately, the group would help introduce the nation to the possibilities — and problems, like sloppy security protections — that come with computer connectivity. After the group was exposed, member Neal Patrick was asked on NBC’s Today show if he had any regrets.
“In hindsight, I really wish that accessing those systems just wasn’t so easy,” he replied.
Whiz Kids
In the early 1980s, computer culture was having a moment. The first IBM personal computer came on the scene in 1981, popularizing the term PC. The next year, the Commodore 64 was introduced; it would later become the best-selling computer model of all time. By 1983, both tech aficionados and more cautious adapters were warming up to the PC’s potential. That same year, The New York Times went digital with the organization’s first newsroom computer.
By today’s standards, however, these simple machines still had a long way to go. “One of the most relevant things here is just how early this was in the technology age,” says Alan J. Borsuk, who was a reporter at The Milwaukee Journal at the time and covered the 414s. “It was before there was a popular concept of the internet or email or anything like that. It was really very rudimentary — just the beginnings of things.”
But for many, these proto-computers were a portal into previously uncharted territory. Tim Winslow, who would become a member of the 414s, first tapped into their potential as a junior high school student in the mid-1970s. His math teacher had brought in a primitive computer to test out some problems. The device, called a teletype, was essentially a mechanical typewriter that displayed text on a glass screen. Combined with an acoustically coupled modem, which transmitted signals through a telephone network, the system was able to send and receive typed messages.

At the time, personal computers like the Commodore 64 were just becoming popular. (Credit: Arda savasciogullari/Shutterstock)
Arda savasciogullari/Shutterstock
Winslow didn’t have a chance to test the computer during class. But he stayed after school that night to try it out for himself. As soon as his teacher dialed into the network and revved up the math program, Winslow was hooked. “I fell in love with just trying to learn and create with this new technology,” he says.
Winslow found he wasn’t the only one who gravitated to these early computers. In high school, he joined an Explorer Scout program focused on computing and tech, sponsored by IBM, where he met most of his fellow would-be hackers. The members met right after school in downtown Milwaukee to program computer code together.
Over time, many of them became friends, eventually deciding their group needed a name. In the 1980s, gangs in Milwaukee would identify themselves by the names of the streets they ran, like the 2-7s, who were active on 27th Street — numbers that were carved on the picnic tables where the hackers sometimes met for dinner. Since their turf was Milwaukee, the group took its name from the local area code and became “the 414s.”
Let the Games Begin
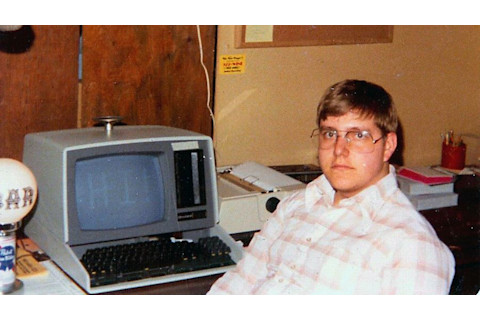
Tim Winslow was among the 414s interviewed for the documentary The 414s: The Original Teen Hackers, which premiered at the 2015 Sundance Film Festival. (Credit: Winslow Family)
Winslow Family
Over at least a year, the 414s used their home computers and telephone modems to connect to major computer installations across the country. By using basic passwords and login information — which were written in the instruction manuals for various computer systems and never updated or changed — they were able to penetrate these larger networks. For example, says Winslow, the login and password for one of the systems were simply that: system and system.
“It was so easy to get logged into them because people didn’t read their own manuals,” he says.
The gang saw themselves as explorers, harnessing their curiosity to learn more about how the systems worked. Mostly, the 414s were looking to get their hands on computer games. Throughout 1983, though, the group’s activities grew bolder. At one point, they hacked into Security Pacific National Bank in Los Angeles, which had billions in assets. That spring, the 414s infiltrated a computer at Los Alamos National Laboratory.
By June, the jig was up. The 414s’ exploits were revealed when they hacked into Memorial Sloan Kettering and accidentally deleted billing records. This tipped off a Memorial Sloan Kettering administrator, who then contacted the FBI, which tracked the gang back to Milwaukee by tracing incoming telephone calls.
“In order to get more proof, they actually went outside of our homes and put data-capture pieces [on] our phone lines,” says Winslow. Not long after, several of the 414s, including Winslow, then 20; Gerald Wondra, 21; and 17-year-old Patrick would be greeted by suit-and-tie-clad FBI agents on their doorsteps.
“I had gone to bed a little late the night before; my mom came down and woke me up,” says Winslow, who came upstairs to find the agents sitting at the kitchen table. “They [said], ‘We’d like to talk to you about what you’ve been doing with your computer for the last few months.’"
A Hidden Legacy
Winslow, Wondra and another member were all charged by the federal government and faced the possibility of jail time. But because Patrick was a minor, he wasn’t at risk for prosecution.
(Credit: Michael T. Vollmann)
Michael T. Vollmann
While his peers made plea deals, Patrick toured the media circuit, appearing on The Phil Donahue Show and the CBS Morning News. His face was splashed across the cover of Newsweek. He even testified on the dangers of computer security before Congress in Washington, D.C., where the clicking of cameras was so loud that it sometimes drowned out the people speaking. At one point, Patrick was asked when he first considered the “ethical propriety” of what he was doing.
“Once the FBI knocked at my door,” he answered.
Because there were no laws against hacking at the time, the adult members of the 414s were charged with making harassing telephone calls. The misdemeanor offense came with two years of probation and a $500 fine; the charges were eventually expunged.
Yet, nearly four decades later, the 414s’ legacy lives on — though perhaps not in the most obvious ways. Filmmaker Michael Vollmann, director of the documentary The 414s: The Original Teenage Hackers, says he was originally drawn to the group’s story because it has since been overshadowed by films like WarGames. “[But] there were a few things that came out of it,” he continues. “Like the fact that Neal Patrick went and testified before Congress to talk about his experience.” As a result of the gang’s exploits, and the media circus that followed, six bills were introduced in the House that dealt with different aspects of computer crime.
Morgan Wright, a cybersecurity expert, notes how far the field has come since. “We’ve come a long way [from] the curiosity of kids that just looked at it and said, ‘Hey, let’s just try passwords,’ ” he says. “That was really the only protection; [there was] no two-factor authentication, no security tokens, no digital certificates. All of that came later, and it came when we could no longer trust people with just a username and password because it was too easy to break in.” Ultimately, he says the story of the 414s was a watershed moment that exposed the soft underbelly of computer security.
“If it is the case that these were the only people who got into Los Alamos labs when it was very poorly protected,” adds cybersecurity expert Joseph Steinberg, “[then] they did us a big favor.”